Information Security Audit Service
In today's information-driven era, data is held in high regard, and its security is paramount. Nonetheless, unscrupulous individuals exploit vulnerabilities in a business's security infrastructure for their gain. To maintain the highest level of security in your enterprise, a comprehensive security audit is essential. To perform such an audit, it is advisable to engage the services of a professional IT security auditing firm, such as Version Next Technologies. Our team comprises skilled experts with a track record of conducting IT security audits for esteemed clients in Mumbai.
When it concerns the safeguarding of your business's data and information, there can be no room for compromise. IT security auditing firms like Version Next Technologies conduct thorough audits and deliver comprehensive reports for your prompt action. Additionally, we offer a comprehensive array of security services to meet all your needs, including Vulnerability Assessment and Penetration Testing (VAPT) services, as well as web application security testing services, among others.
In line with our commitment to excellence across all our services, we employ the most advanced methodologies when conducting audits, ensuring that the resulting reports are characterized by minimal to negligible errors. Our cyber security audits are instrumental in revealing the vulnerabilities within your system and shedding light on existing security loopholes. Our seasoned professionals, boasting years of experience in this field, possess a unique skill set that sets them apart. Their extensive expertise allows them to conduct audits in a manner that surpasses the capabilities of professionals at other security firms. This cadre of exceptionally talented security experts is the cornerstone of our competitive advantage.


Prior to initiating an IT security audit for your organization, it is imperative to establish a clear set of objectives to be accomplished. We maintain unwavering professionalism in all our endeavors and adhere rigorously to the standards we have set for ourselves. Once the audit objectives are defined, we dedicate our full commitment to their fulfillment, ensuring that you receive the anticipated outcomes from the audit. This operational approach has positioned us as a premier IT security auditing firm in India and underscores why numerous prominent brands have entrusted us with the security of their organizations. We remain resolute in our efforts to sustain the highest level of service quality possible.
Our comprehensive audit encompasses the entire spectrum of security, addressing aspects ranging from network vulnerabilities and control issues to encryption-related concerns, and much more. Our primary responsibility is to ensure that every pertinent detail is meticulously documented in the audit, ultimately enhancing the security posture of your business.
In the realm of IT security services, Version Next Technologies stands as the foremost security service provider in Mumbai. Our deep understanding of security sets us apart from the rest. These factors provide further justification for placing your trust in the quality of our services and selecting us whenever your company requires an IT security audit.
Our Methodology
Version Next Technologies's information security assessment program represents a unique fusion of the most acclaimed practices in information security management standards. Our IS audit program is the result of amalgamating various standards and the accumulated expertise of our specialized teams over the years. Additionally, our vulnerability assessment and penetration testing (VAPT) methodology is a meticulously documented and repeatable security assessment approach. This methodology is continuously updated to align with evolving threat landscapes and industry best practices, ensuring consistency and structure in our information security audits and VAPT services.
Our VAPT Certification Methodology
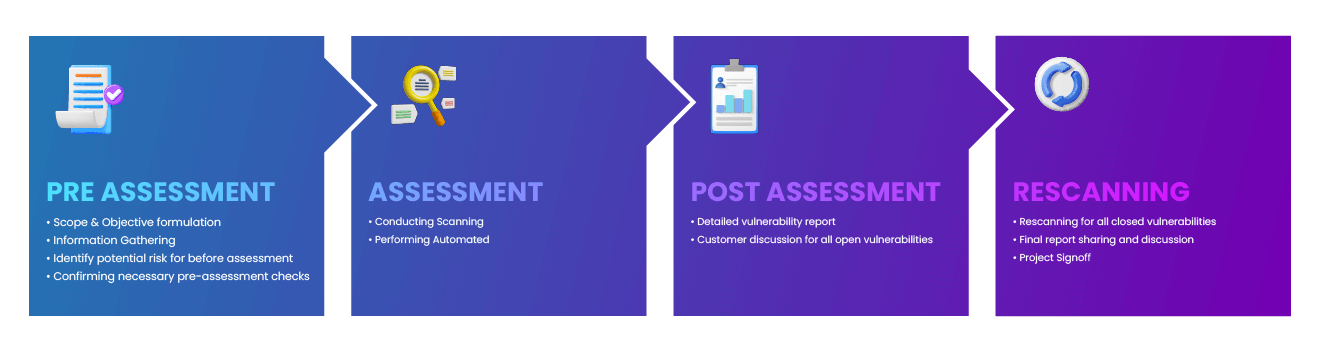
Version Next Technologies is committed to staying one step ahead by regularly enhancing our IS program and techniques with new tools, processes, and emerging trends. Our methodology encompasses a comprehensive blend of the following methodologies and industry best practices in IT security:
- ISO 27001:2013 Information Security Management Standard
- ISO 22301:2012 Business Continuity Management Standard
- PCI-DSS v3.2, PA-DSS
- NIST SP 800-115 Technical Guide to Information Security Testing and Assessment
- HIPAA (Health Protection & Prevention Act) and/or Data Privacy Law
- Open Source Security Testing Methodology Manual (OSSTMM) from the Institute for Security and Open Methodologies (ISECOM)
- SANS Security Controls
The IS audit encompasses various facets, including audits of network devices, network support services, application security, hardening audits for operating systems and databases, process audits, evaluations of non-technical controls, operational management assessments, reviews of Business Continuity Planning (BCP) and Disaster Recovery (DR) measures, and compliance mappings. Additionally, it includes capacity planning for the integration of information security into new projects.
When conducting the network devices audit, we evaluate a range of devices, including but not limited to those listed below. Our audit approach prioritizes minimal grants and privileges configurations, adhering to a need-to-know basis principle from the outset.
The purpose of an IS Audit is to evaluate the effectiveness of security controls and their implementation status on the target systems. This audit involves examining various system hardening parameters in comparison to organizational guidelines, industry best practices, or recommended standards. These audits aim to identify security vulnerabilities that may result from insecure default settings from vendors, the absence of security patches, security misconfigurations, and similar issues. Version Next Technologies conducts this audit using a combination of automated tools and manual auditing techniques.
Our auditing process adheres to common industry best practices and recommendations, which serve as a baseline for our assessments. These include:
- CIS Security Benchmarks
- DISA Security Guidelines
- CERT Guidelines
- SANS Security Guidelines
- NIST Security Guidelines
- Hardening Guidelines from Cisco, Oracle, and Microsoft.